Harman says that the prospect of cyber attacks on vehicles is becoming an increasingly serious one as vehicle connectivity is being enhanced and it has developed what it claims is an appropriate framework to deal with the threat.
More and more users are embracing the ‘connected car’ and, in theory at least, any form of wireless link – even via a separate mobile phone or tablet – could provide the conduit that hackers need to launch an attack.

Discover B2B Marketing That Performs
Combine business intelligence and editorial excellence to reach engaged professionals across 36 leading media platforms.
“A few years ago the concept of automotive cyber security was largely confined to industry experts,” says Harman’s Asaf Atzmon, Director, Business Development and Marketing, Automotive Cyber Security. “Now it’s a topic that consumers are asking about. According to a recent survey, in some countries as many as 59 per cent of buyers are actively concerned about the prospect of car hacking.”
There seems to be a unique brand of fear associated with the idea of car hacking, Harman points out – it could mean brakes jammed on in the middle of the motorway, headlights disabled in the dead of night or the car stereo suddenly playing Justin Bieber. None of it bears thinking about.
Harman also notes that to date, there hasn’t been a single instance of malicious car hacking – the examples that have made the headlines all involved engineers or researchers experimenting under controlled conditions. In most cases it also required a cable to be physically plugged into the car.
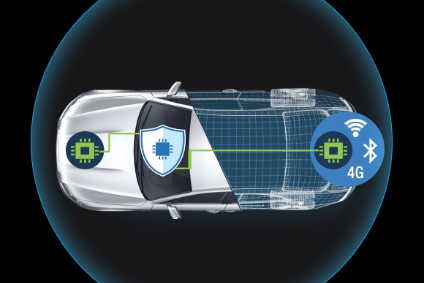
Harman has devised a specially-developed 5+1 security framework which consists of a series of layers that protects the car’s head unit from being compromised and used as a portal into the in-vehicle network (something which could jeopardise safety critical systems). It can be thought of like the layers of an onion:
- At the deepest level, a secure hardware platform provides a safe place to store cryptographic keys and execute highly-sensitive operations in a secured manner.
- Safety-critical functions are isolated from the infotainment system using what’s known as a hypervisor. This concept – originally developed for supercomputers – allows two completely separate operating systems to run off the same hardware. It makes it extremely difficult for an infection on one side of the system to spread to the other.
- The next level controls access to the memory, storage and peripherals. It essentially determines who has access to what. If, for instance, your CD player suddenly wants to control the brakes it’s a good indication that something is wrong.
- Next comes the sandbox function. This keeps newly downloaded applications separate from the core system so they can be disabled and removed if they’re found to be harmful.
- The fifth level is the network protection system. This controls the flow of information into and out of the car, looking for any signs of intrusion. Working on two levels, ECUSHIELD turns the vehicle’s ECU into an Intrusion Detection and Prevention (IDS/IPS) system and smart firewall to protect critical communications within the car. It continuously monitors the vehicle to provide real-time detection of malicious communications and prevents them from reaching the vehicle’s critical systems. Meanwhile, TCUSHIELD protects infotainment and telematics systems. Also using IDS/IPS technology, it integrates with existing telematics units and uses highly advanced algorithms to protect both internal and external networks so a vehicle can operate safely while still monitoring and reporting to an external control centre. This level has the ability to spot patterns and uncover a threat, even if the threat is attempting to disguise itself as a legitimate function such as a software update.
- The final ‘plus one’ level is the ability to install over-the-air (OTA) updates to various systems within the car such as the navigation, engine management and infotainment systems. By keeping the software up to date, it helps to ensure that the car is protected at all times.
It is claimed that all of these elements combine to produce a virtually “impenetrable shield around the safety-critical functions” and those which may contain personal data, such as credit card information. Haraman says it is already working with a number of car makers to employ this technology on future models.
“Ultimately, it’s all about eliminating the risk of intrusion,” says Atzmon. “The car industry will need to reassure consumers that their connected cars are safe. By 2020 it’s expected there will be nearly a quarter of a billion of them on the world’s roads. This number will continue to grow but only if the car industry can provide the protection that those consumers have to come to expect from their other electronic devices.”






