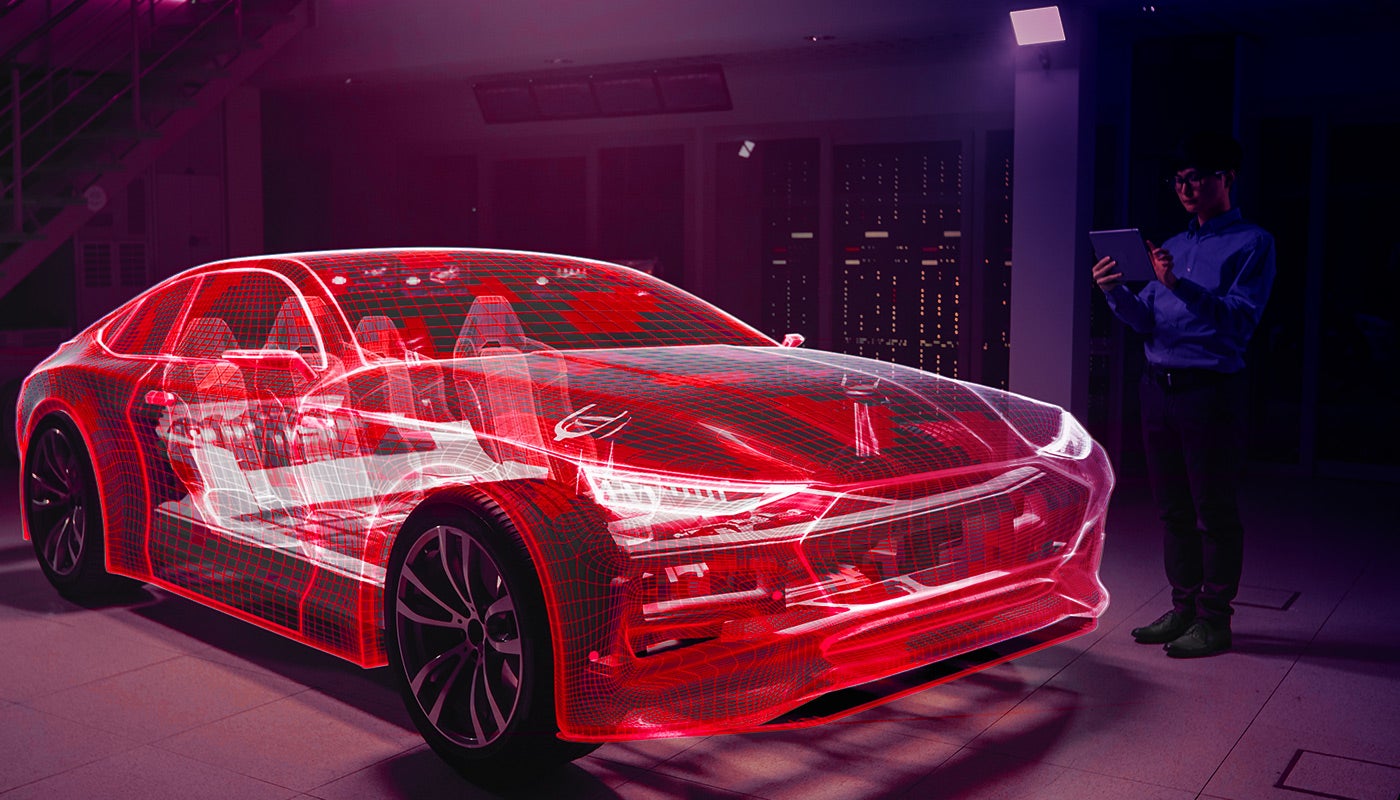
With technology in today’s vehicles increasing and improving with each new launch, although a positive for the automotive customer, this also provides more opportunities for cyber-criminals to hack into onboard technology.
An American electronics and measurement equipment manufacturer, Keysight Technologies, has been working extensively within the automotive industry in order to combat the risk of cyber-attacks.

Discover B2B Marketing That Performs
Combine business intelligence and editorial excellence to reach engaged professionals across 36 leading media platforms.
The company supplies test capability technology to automotive manufacturers and component suppliers, allowing them the ability to replicate and test attacks on a connected car in a multitude of ways.
We spoke to Scott Register, vice president, security solutions, Keysight Technologies, to find out more about this technology and learn more about the current cybersecurity risks the industry is facing.

Just Auto (JA): Could you provide me with some background on the company and your role?
Scott Register (SR): Keysight is one of the world’s largest suppliers of test and measurement solutions. We provide all the things that designers and manufacturers use to accelerate innovation and bring better products to market, faster.
Keysight is a spin-out of Agilent which is a spin-out from Hewlett Packard. We do everything from battery drain analysis to 5G signalling compliance to RF interference testing to cybersecurity validation.
I’m the vice president of Security Solutions, and my role is helping us bring security validation to new areas of our business such as automotive.
What solutions/technology does Keysight Technologies provide the automotive industry when looking at cybersecurity?
Keysight is in a unique position in the industry. I think we’re the only company that brings so many diverse technologies and capabilities under a single roof.
For example, we already supply a lot of test capability to automotive manufacturers and component suppliers, including complete LTE, 5G, and upcoming 6G connectivity capabilities. We can combine those technologies with our security testing capabilities which we’ve been developing since 2005.
I don’t know of any other single company that can give you the ability to replicate and test attacks on a connected car in a multitude of ways, everything from protocol fuzzing against the radio protocols to application-level attacks for Bluetooth and CAN bus and Wi-Fi and cellular.
We even provide an integrated solution which lets you direct advanced attacks against the car over your choice of mobile protocols from a single product with integrated security and cellular network capabilities.
When looking at cybersecurity what are the most prominent threats presented to the automotive industry?
That’s a great question, and it’s changing over time. Right now, the biggest threats are probably compromises to an individual vehicle: Opening door locks via a Bluetooth hack or stealing payment information in an electric vehicle (EV); or manipulating ADAS (Advanced Driver Assistance System) to cause a car to do something unsafe while operating. But as cars become more autonomous and interconnected, then the potential for mass mayhem increases.
Imagine if you can clog a city grid by telling every car on the street to stop, or directing first responders away from an emergency, or use cars as the basis for a DOS attack against a city’s 5G infrastructure in an updated Mirai botnet attack?
We shouldn’t overlook the possibility of an attacker exploiting car owners or manufacturers by pushing a malicious firmware update that causes an EV’s batteries to overheat and catch fire. Most of the hackers with the best funding and protection are sponsored by state actors, so think about the ways a well-funded adversary could cause disruption or steal data for economic benefit and you’re on the right track.
Are newer vehicles and EVs more at risk?
Absolutely. Modern cars have far more computing capacity than the space shuttles, which means they have services that can be exploited.
In addition, the attack surface for cars is expanding dramatically. A few short years ago, the only real way to connect to the “brains” of a car was via the On Board Diagnostics (OBDII) port which could give you access to a car’s Car Area Network (CAN bus), and that required specialised interfaces and physical access to an unlocked car.
Now, we’ve added not only USB interfaces but also Bluetooth, Wi-fi, and cellular interfaces, which open the car up to attack by anyone within radio range or beyond.
In short, there’s more to exploit and more ways to exploit it, and there’s much more valuable onboard data. We’ve already seen examples of everything from unlocking doors to steering cars off the road, and as more aspects of a car’s operation are controlled by computer, inevitably there are more things that can be hacked.
What more do you think the industry could/should be doing when looking at cybersecurity threats?
There’s been more focus recently on security compliance in the automotive space, driven by requirements such as the United Nations Economic Commission for Europe (UNECE) R155 and R156 that set a framework for automotive cybersecurity.
That’s a good thing as it raises visibility on the issue, but it’s well understood in the cybersecurity field that compliance is not security. We feel strongly that consumers will be much safer if automakers become much more proactive about actually testing their vehicles – trying to hack into their cars the way real bad actors will, and get ahead of hackers by fixing vulnerabilities before they’re exploited in the wild.
What do you see the future holding for this issue?
Historically, people tend to overlook the potential for a significant cybersecurity event until something big happens, and then there’s a correction and we start paying attention.
IoT security, for example, received much more attention after the world’s largest botnet attack to date, Mirai, took over webcams and set top boxes and took down big chunks of the Internet.
Ransomware was a big of a fringe issue until it became mainstream. I think there will be a few headline-making automotive cybersecurity breaches in the real world, not just lab proof-of-concept disclosures, before the industry intensifies focus.
Hopefully whatever happens won’t be too destructive and the industry will respond quickly. Fortunately, we’re working with a number of manufacturers who are actively working to stay ahead of these challenges and close any vulnerabilities before anything happens.






